Sending a follow-up email just after the first one was opened increases your reply rate by 80%.
Add the famous read receipt in your Gmail
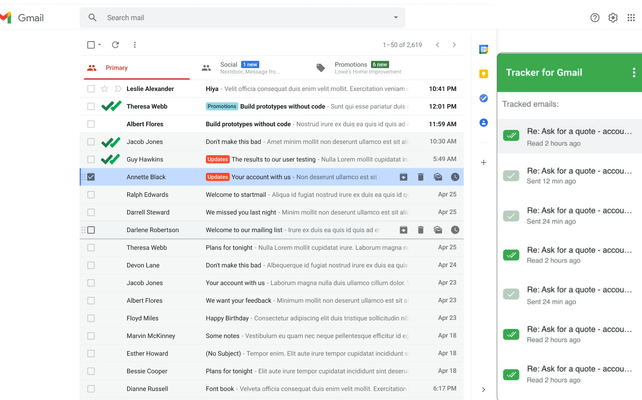
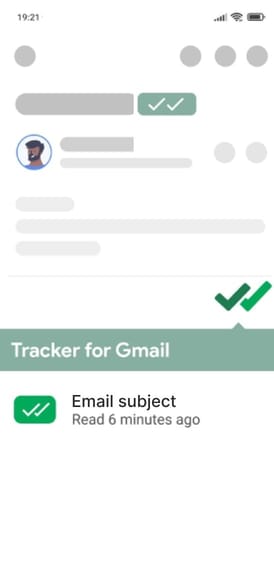
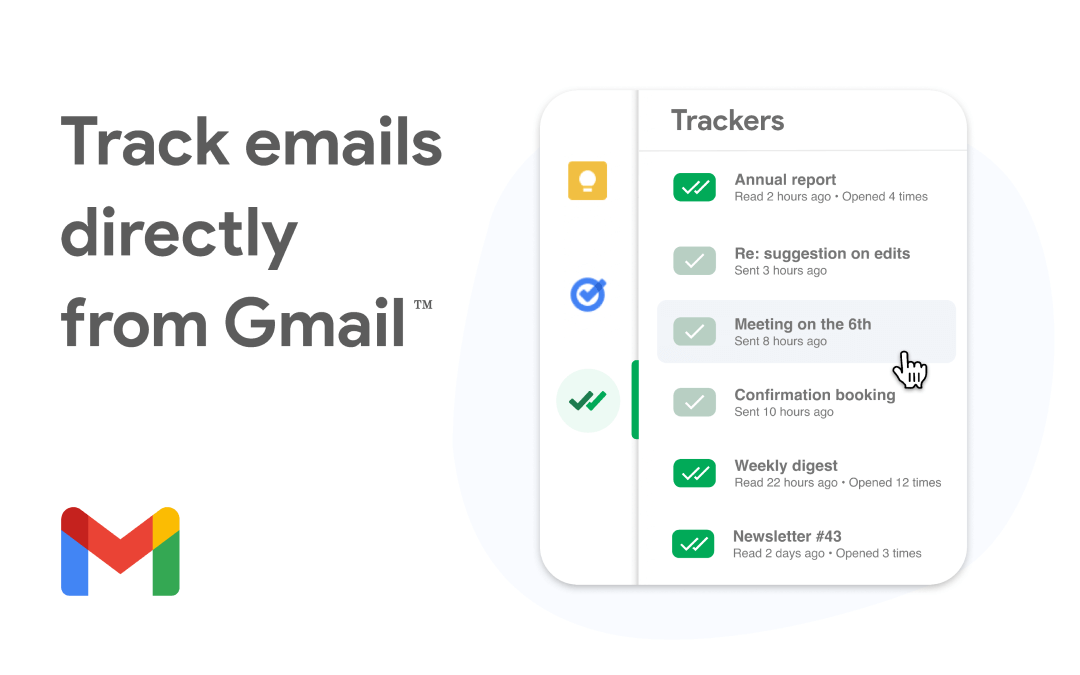
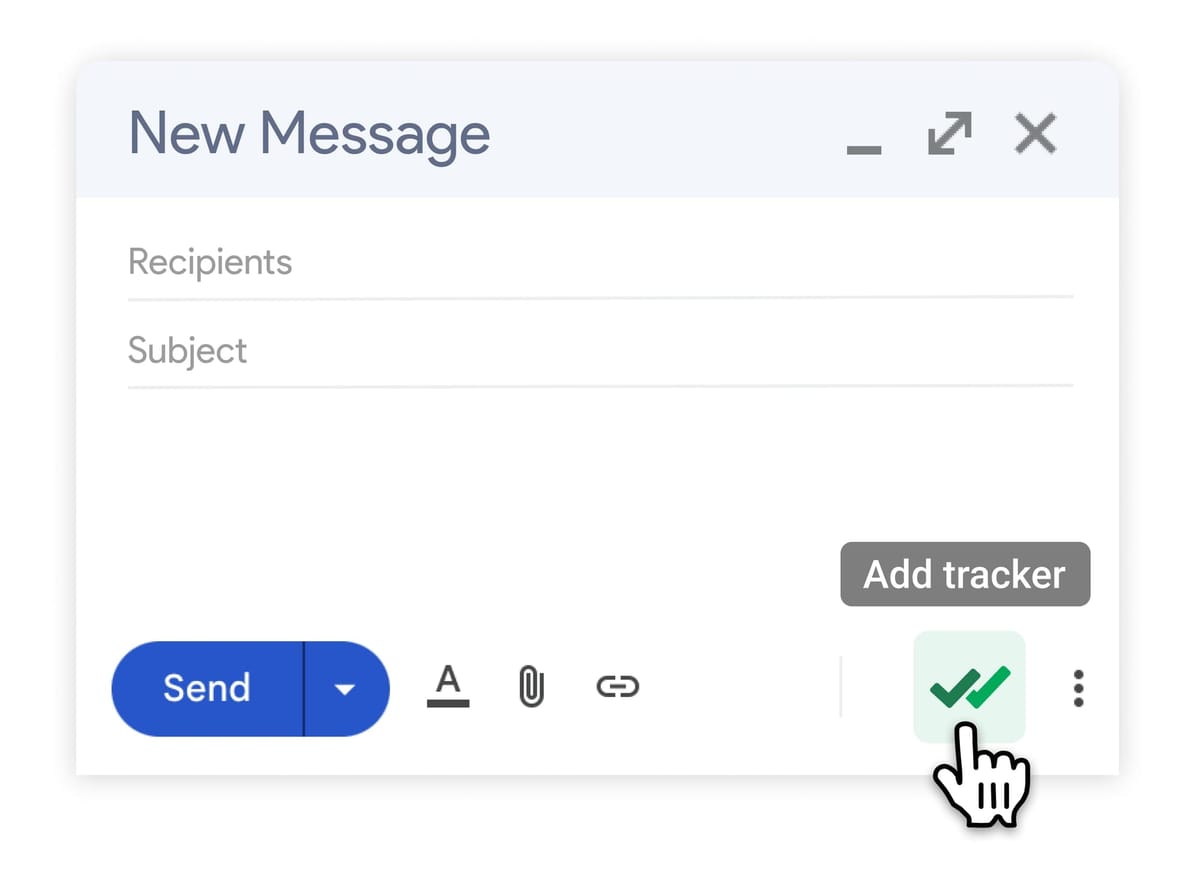
Receive an instant notification as soon as your email is opened
For each tracked email, get a list of all the time it was opened
Your privacy matters: we can’t read your emails. Learn more:
https://mailtrack.email/security
Companies and organizations from all over the world trust Mail Track for Gmail










See what your clients say about us
A cut above the rest of the email tracker for gmail software available. Super easy to use and a generous free plan. Plus, importantly, it doesn't request permission to read my emails.
One of the best email tracking to know when our important emails are opened.
Always know what you will pay
| Free | Premium | |
|---|---|---|
| $0$0 | $2.99$5.99 | |
| / month/ month | / user / month/ user / month | |
| Tracked emails per day | Unlimited | Unlimited |
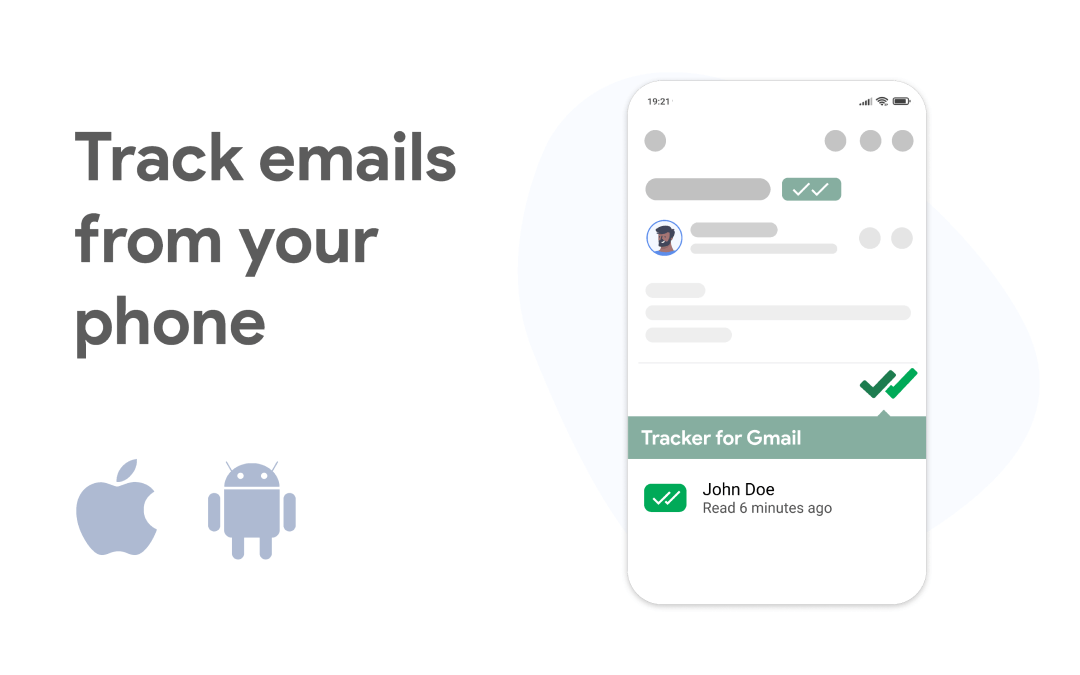
| Track from mobile | ||
| Mail notifications | ||
| Remove Mail Track Branding | ||
| Real time notifications | ||
| Team Plan | ||
| Get startedGet started | Get startedGet started |
If your blog post is for a technical audience, you should reference specific IoCs typically found in reports like those on ORKL : choziosi[.]xyz
The malware connects to Command and Control (C2) domains (e.g., choziosi[.]xyz ) to receive further instructions or download additional payloads like info-stealers or miners. File: The.Jackbox.Party.Pack.7.zip ...
Often drops the RedLine Stealer or Vidar Stealer , which aim to harvest browser passwords, credit card info, and crypto wallets. 4. Safety Tips for Readers If your blog post is for a technical
It frequently checks for virtual machines or debuggers to hide from security researchers. 3. Key Indicators of Compromise (IoCs) Safety Tips for Readers It frequently checks for
Threat actors capitalize on the high search volume for free versions of popular software.
Often masquerades as legitimate system processes or uses randomized strings.
Before running suspicious files, use tools like VirusTotal to check for malicious detections.
Install our free mailtracker now