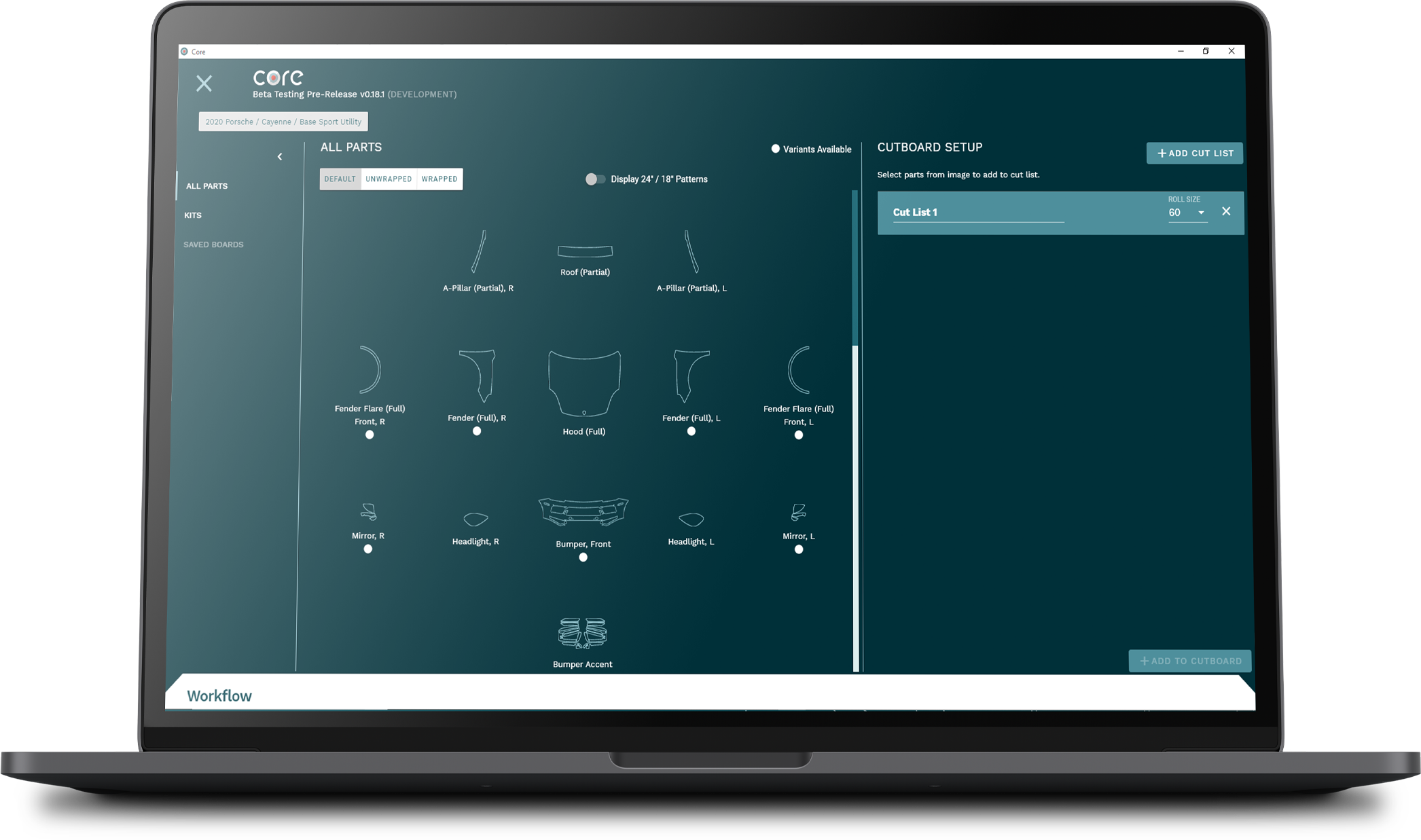
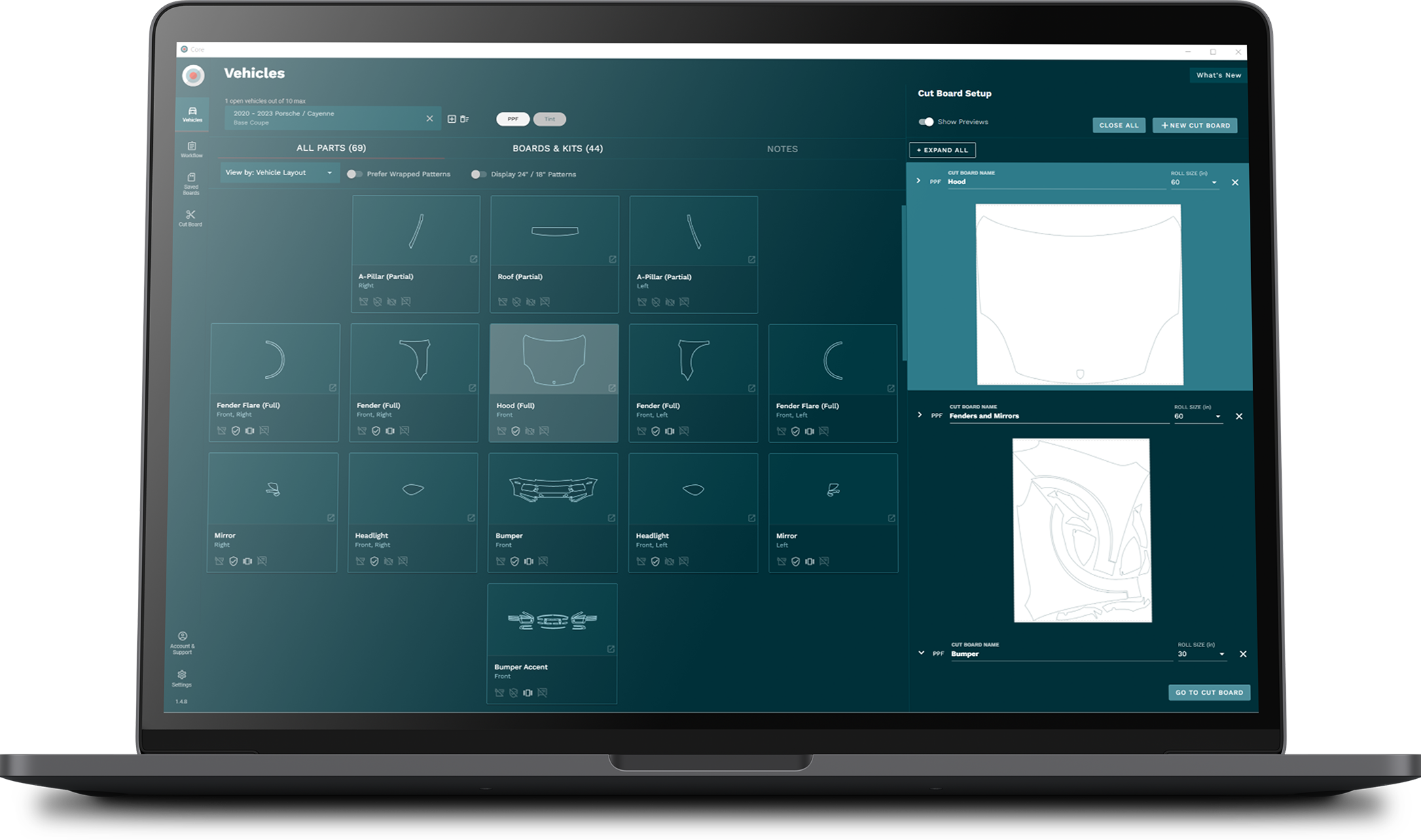
SMARTER, FASTER, BETTER PATTERNS

Global team of dedicated
pattern designers

Thousands of time-saving PPF and window film patterns
Verified pattern process for accuracy and
efficiency

Scanning technology for fast,
precise pattern creation